Sovereign Security for Canadian Municipalities
Protecting civic infrastructure with northamerica-northeast1 residency, Assured Workloads policy enforcement, and encryption at rest with Customer-Managed Encryption Keys (CMEK).
Trusted Compliance Standards
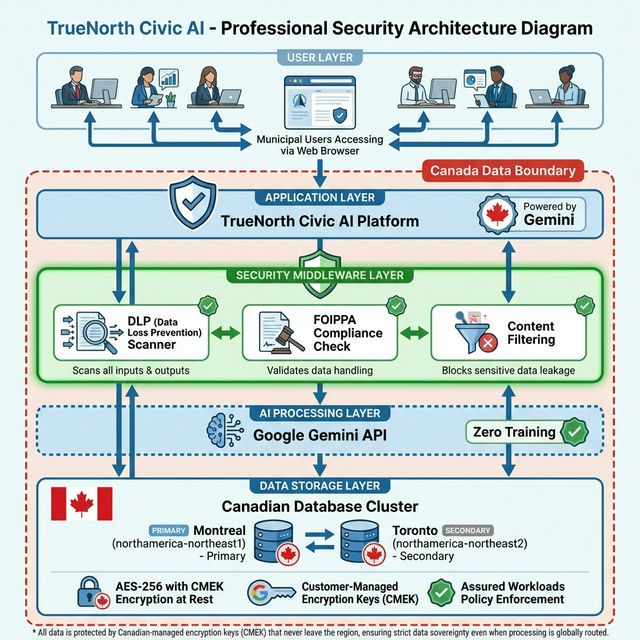
Defense-in-Depth Architecture
Our platform employs specific technical controls within the Google Cloud "Canada Data Boundary" to ensure data never leaves Canadian jurisdiction.
Technical Residency
Primary infrastructure is hard-pinned to northamerica-northeast1 (Montreal). All data is protected by Canadian-managed encryption keys (CMEK) that never leave the region, ensuring strict data sovereignty even when processing is globally routed.
Policy Enforcement
We utilize GCP Assured Workloads to apply organization-level policy constraints. This automatically blocks the creation of any resources (VMs, Buckets, DBs) outside of approved Canadian regions.
Encryption at Rest
All data is encrypted at rest using Customer-Managed Encryption Keys (CMEK) with AES-256 encryption. We maintain exclusive control over our cryptographic keys, ensuring true data sovereignty within Canadian data centers.
Canada Data Boundary
Part of our Assured Workloads control package, strictly enforcing the Canada Data Boundary. This includes restricting resources to Canadian regions and enforcing minimum TLS versions for all transit.
DLP Privacy Middleware
Every prompt is intercepted by our Cloud DLP API before reaching the AI model. We use Canadian-specific inspection templates to detect and redact:
Security Architecture Overview
A comprehensive view of our defense-in-depth approach, showing how data flows through Canadian infrastructure with DLP scanning and FOIPPA compliance at every layer.
Hosted Exclusively in Canada
To address the threat of the US CLOUD Act, we maintain strict Jurisdictional Control. Our architecture ensures data remains securely within Canadian jurisdiction via CMEK encryption, aligning with FOIPPA.
- check_circle
Primary: northamerica-northeast1
Montreal based low-latency clusters.
- check_circle
Failover: northamerica-northeast2
Toronto based disaster recovery.
- shield
Jurisdictional Control
Decryption keys managed separately from data.
Frequently Asked Questions
How do you mitigate the US CLOUD Act?expand_more
We mitigate this risk through strict technical and jurisdictional control. By hosting data strictly within Canadian borders using GCP Assured Workloads and encrypting all data at rest with Customer-Managed Encryption Keys (CMEK), we ensure that data remains protected within Canadian jurisdiction. Our primary storage and encryption infrastructure is hard-pinned to Montreal, preventing unauthorized data egress to foreign nodes, even when processing is globally routed.
How is municipal data isolated?expand_more
We use strict logical tenant isolation within our database clusters. Every query is scoped to a specific Tenant ID, ensuring that cross-contamination of municipal records is impossible at the database level.
Do you conduct penetration testing?expand_more
Yes. We engage independent third-party security firms to conduct penetration testing on our application and infrastructure twice annually. Summarized reports are available to enterprise customers upon request.
How are project documents protected?expand_more
Project documents are isolated by user, scanned by Cloud DLP before ingestion, and stored in Canadian-only GCP regions. Access is controlled at the project level within your specialized task workspace, ensuring that your research and data remain secure and isolated.